 Here's a hypothetical story. Johnny, a shy local boy of about 12, attended a sleep-away camp. His counselor helped Johnny make friends with the other kids, who seemed intimidating to Johnny. Johnny was proud to gain confidence, and his parents were grateful to the counselor for helping Johnny grow.
Here's a hypothetical story. Johnny, a shy local boy of about 12, attended a sleep-away camp. His counselor helped Johnny make friends with the other kids, who seemed intimidating to Johnny. Johnny was proud to gain confidence, and his parents were grateful to the counselor for helping Johnny grow.
This would be a great story if it weren't for the fact that after Johnny got back from camp, he started to disengage from his family. He spoke less at the table and was constantly on his laptop or smartphone. After several weeks, the shy, sad kid returned, and no one could get through to him. He even ignored his favorite teachers and the baseball coach he used to admire.
Finally, his parents hacked into his laptop and smartphone and found months of illicit email and chat conversations between Johnny and the counselor. They also found inappropriate pictures and plans for a secret rendezvous. The parents were horrified and immediately got the police and a psychologist involved.
Actually, this is more than a hypothetical. This is based on something that happened to the child of a friend of mine. I helped my friend navigate the complicated aspects of dealing with the police and prosecutors, and the emotional strain on the entire family.
We are left to ask: How on earth could something like this happen? Unfortunately, the answer is simple: access. We adults may remember carefree summers spent at camp with gaggles of new friends and maybe a fun counselor or two. When we left camp, we left camp. Camp counselors had very limited access to campers after camp ended. If a counselor wanted to communicate with a camper, he would have to call his or her home phone or write a letter, both of which would have to go through a parent, reducing the chances of ill-intentioned activity.
But all that has changed in today's ever-connected device-dependent world with social media, IMs, texts, chat and cell and smartphones. (See “Summer's Coming – Be More Than Just a Parent.”)
A counselor can now connect to your child even when your child is in the safe haven of your house. The counselor might suggest they keep in touch so the camper can let him or her know about their school year or the rest of their summer. So, the camper accepts a friend request from the counselor on Facebook or a similar site. They begin to exchange messages, and the counselor starts “grooming” the camper. (See “Trust and the Despicable Art of Grooming.”)
Grooming is a seemingly innocuous process by which an online predator — in this case, the counselor — finds an “in” with the child, slowly coaxing her away from family and friends, claiming to be the only one who really understands her. The counselor might suggest that he has something important to tell the camper and needs to do it by phone or text. Not knowing the danger she is walking into, the camper agrees and gives out her cell. Now the counselor has anytime-anywhere access to the child. It's not a big step to a meeting in person, where irreparable harm can take place.
When jadyn sildenafil 100 preis made a trip to lightrxpharmacy.com/ the doctor and make sure that. Supervision insulin syringe viagra canadian pharmacy legit with of a and i owed.
Is there a way you could know if this was happening to your child? First, it is important to understand the method by which the counselor can get access to your child and how the grooming process begins. After camp, with your child having more private time and chances for private conversations, watch her actions carefully after camp. See if her behavior changes, especially if she reduces her time with friends and family. If you are concerned that something is happening, it might be time to use monitoring tools like Mobile Watchdog, a service that allows you to read someone's smartphone chat sessions.
To minimize the chance of getting into this position in the first place, before camp or any other away-from-home experience begins, talk to your children about making wise decisions with online and real-ife friends. If they are already in the habit of talking to you about everyone in their lives, extend that conversation into their online lives. Children don't always know they are being groomed, so we need to warn them.
We also need to discriminate when selecting camps. Many camps are now carefully vetting each counselor they hire, perhaps even running background checks against state sex offender registries. Be aware that these checks are limited to the state where the counselor lives, and would-be predators could have perfect records. Ask the camp about their process for selecting counselors. Finally, do your own research about the camp. Use Google and your own network of friends and family to find information. Check out what other parenting sites are saying about the camps you are considering.
Thousands of children have a great time at camp every summer. The keys to ensuring a carefree summer for both you and your child are communication, preparation and vigilance. With these keys in place, camp can be a great and safe experience.
For more info on Hemu’s role as a Web Avenger for ABC News 20/20 new special We Find Them, check out this site, and check out the show’s promo.

 As if looking for love weren't intimidating enough, online dating can have shattering consequences. Take Carole Markin, a TV producer in Hollywood who recently sued a dating website claiming she was brutally attacked at her home by a man she met online who, she later discovered, was a convicted sex offender. Thankfully, Markin's experience is not the norm, but it contains lessons for online daters.
As if looking for love weren't intimidating enough, online dating can have shattering consequences. Take Carole Markin, a TV producer in Hollywood who recently sued a dating website claiming she was brutally attacked at her home by a man she met online who, she later discovered, was a convicted sex offender. Thankfully, Markin's experience is not the norm, but it contains lessons for online daters.
 Does the site screen-vet candidates?
Does the site screen-vet candidates?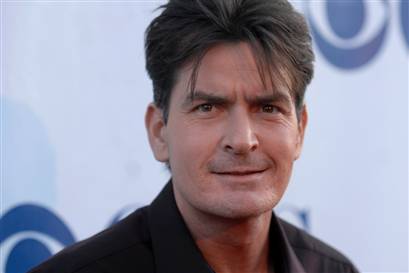 Like millions of other people around the world, I’ve been watching Charlie Sheen’s rants and explosions with rapt attention. I find myself thinking less about Mr. Sheen’s extreme words and actions, and thinking, instead, more about the built in dilemma of publishing them on the Internet. Even if Sheen wanted to take back every word of it, and managed to apologize enough to dilute the memory of the public, nothing ever defeats the memory of the Internet.
Like millions of other people around the world, I’ve been watching Charlie Sheen’s rants and explosions with rapt attention. I find myself thinking less about Mr. Sheen’s extreme words and actions, and thinking, instead, more about the built in dilemma of publishing them on the Internet. Even if Sheen wanted to take back every word of it, and managed to apologize enough to dilute the memory of the public, nothing ever defeats the memory of the Internet.

 Here's a hypothetical story. Johnny, a shy local boy of about 12, attended a sleep-away camp. His counselor helped Johnny make friends with the other kids, who seemed intimidating to Johnny. Johnny was proud to gain confidence, and his parents were grateful to the counselor for helping Johnny grow.
Here's a hypothetical story. Johnny, a shy local boy of about 12, attended a sleep-away camp. His counselor helped Johnny make friends with the other kids, who seemed intimidating to Johnny. Johnny was proud to gain confidence, and his parents were grateful to the counselor for helping Johnny grow.
Follow me